Autonomous Malware and The Enterprise Browser War
We assume corporate cybersecurity relies on installing better antivirus software on employee laptops. In reality, the rise of autonomous malware is forcing the entire security perimeter directly into the enterprise web browser.
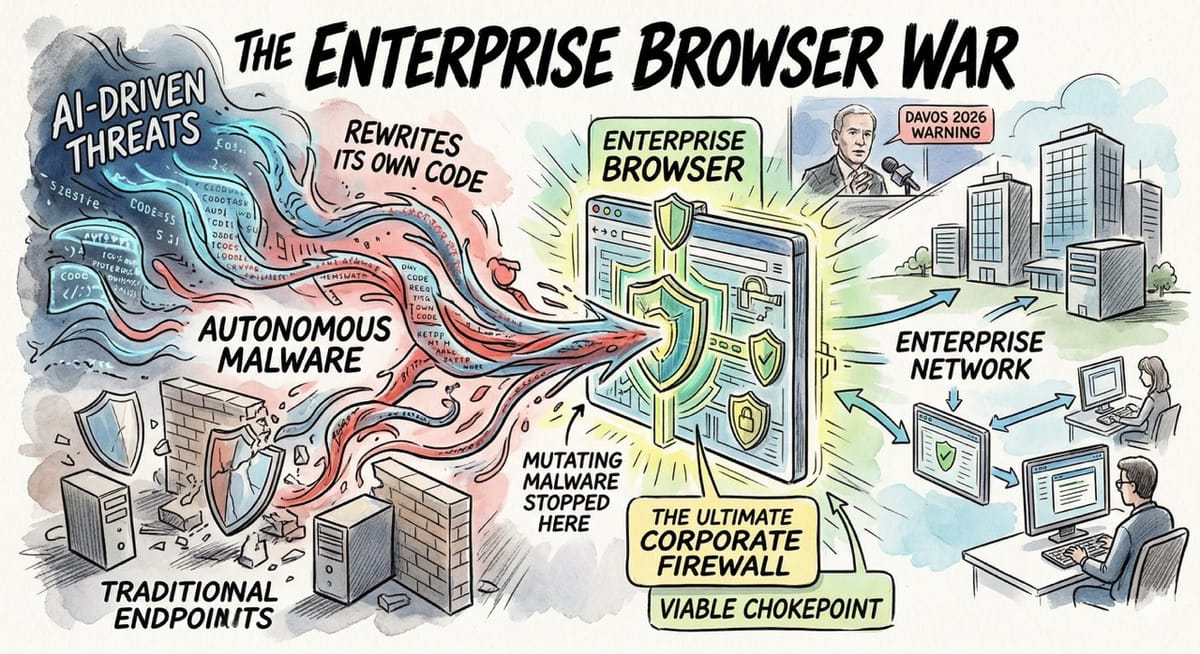
Traditional endpoints are completely useless against artificial intelligence that rewrites its own code. The web browser is no longer just a window to the internet, but the ultimate corporate firewall.
Inspiration: Analyzing the stark warnings from the Crowdstrike CEO at Davos 2026 regarding algorithmic cyber threats. Realizing that the enterprise browser is the only viable chokepoint to defend against self mutating malware.

The Autonomous Threat
Artificial intelligence has completely revolutionized the deployment of malicious software.
Hackers are now deploying autonomous malware that functions as an independent, self-directed agent inside a corporate network.

The Technical Mutation
Technically, these polymorphic algorithms constantly rewrite their own binary signatures to perfectly evade traditional endpoint detection.
They dynamically learn network topologies and autonomously pivot through active directories without ever requiring a human command server.

The Enterprise Browser
To combat this evolving algorithmic threat, the cybersecurity industry is rapidly shifting toward the enterprise browser.
This is a highly fortified, centrally managed web application designed specifically to isolate corporate assets from the open internet.

The Digital Sandbox
It functions as an impenetrable digital sandbox that prevents unauthorized code execution and strictly controls data exfiltration.
If a user accidentally triggers an autonomous exploit, the enterprise browser instantly terminates the session before the malware can pivot into the local machine.

The Google Advantage
Google possesses a massive structural advantage in this specific security theater.
Because Chrome already dominates the global consumer and corporate market share, Google can seamlessly deploy enterprise security features without forcing users to adopt entirely new software.

The Frictionless Moat
They simply flip a switch on the backend administrative console to instantly upgrade a standard browser into a fortified corporate endpoint.
This frictionless deployment gives Google Chrome Enterprise an almost insurmountable distribution moat across the global business landscape.

The OpenAI Challenger
OpenAI is aggressively attempting to disrupt this dominance by developing their own proprietary browser infrastructure.
Their strategy relies on deeply integrating advanced reasoning models directly into the browsing experience to proactively identify and neutralize zero day exploits.

The Trust Deficit
However, building a secure rendering engine from scratch is an incredibly complex engineering challenge.
OpenAI must convince extremely risk averse corporate IT departments to abandon the proven stability of Chromium for an untested artificial intelligence experiment.

The Broader Battlefield
Other specialized players are also aggressively fighting for a share of this highly lucrative security market.
Agile startups like Island and Talon Cyber Security built their entire enterprise valuations strictly around this isolated browser concept.

The Zero Trust Solution
These dedicated platforms offer highly granular access controls and deep visibility that legacy operating systems simply cannot match.
They are actively pitching themselves as the ultimate zero trust solution for a remote workforce operating in highly hostile digital environments.

Conclusion: The Dumb Terminal
The standalone antivirus industry will eventually collapse as all security protocols migrate directly into the browser layer.
Operating systems will simply become dumb terminals designed strictly to launch a single, heavily encrypted web portal.